如何在 Ubuntu 20.04 上安装 Redis
本教程适用于这些操作系统版本
- Ubuntu 18.04(仿生海狸)
在此页
- 第 1 步 - 安装 Redis 服务器
- 第 2 步 - Redis 服务器基本配置
- 第 3 步 - 保护 Redis 安装
- 1。网络安全
- 2。密码认证
- 3。禁用危险的 Redis 命令
- 1。测试主机和身份验证
- 2。测试禁用/重命名命令
Redis 是一种开源的内存中键/值存储,用作数据库、缓存和消息代理。它是一个分布式内存键值数据库,具有可选的持久性。它支持常见的数据结构,例如字符串、哈希、列表、集合、位图、排序集合、HyperlogLogs、流和具有半径查询的地理空间索引。
在本教程中,我们将向您展示如何在 Ubuntu 20.04 LTS 上安装和配置 Redis 服务器。我们将首先安装 Redis 服务器,然后确保安装安全,使其可以投入生产。
先决条件
对于本指南,我们将在具有 1GB RAM 和 2CPU 内核的 Ubuntu 20.04 上安装 Redis 服务器。这仅用于测试,您的生产需要更多。
我们将要做什么:
- 安装 Redis 服务器
- Redis 服务器基本配置
- 保护 Redis 服务器
- 测试
第 1 步 - 安装 Redis 服务器
首先,我们将更新 Ubuntu 系统上的所有存储库并升级所有软件包。
运行下面的 apt 命令。
sudo apt update
sudo apt upgrade之后,使用下面的 apt 命令从官方 Ubuntu 存储库安装 Redis-server 包。
sudo apt install redis-server安装完成后,会出现Redis服务启动失败的错误信息,忽略该错误信息,我们将在下一步进行配置。
第 2 步 - Redis 服务器基本配置
在此步骤中,我们将设置基本的 Redis 服务器。在 Linux 系统上,Redis 配置位于 /etc/redis 目录。
进入 /etc/redis 目录并使用 vim 编辑器编辑配置文件 redis.conf。
cd /etc/redis/
vim redis.conf首先,我们需要选择一个绑定 IP 地址来运行 Redis 服务。 Redis服务不建议使用公网IP,或者如果你运行的是多/集群Redis服务,应该使用内网。
在此示例中,使用本地主机 IP 地址更改绑定地址。
bind 127.0.0.1之后,我们需要设置 Redis 服务如何在服务器上运行。由于我们使用的是 Ubuntu 服务器和 systemd,所以我们需要将监管线路配置更改为 systemd。
supervised systemd保存并关闭。
现在重新启动 Redis 服务并将其添加到启动时间。
systemctl restart redis-server
systemctl enable redis-server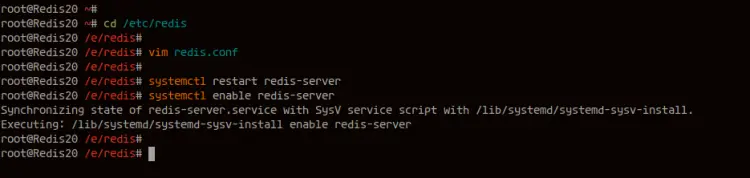
现在确保没有错误,然后检查其状态。
systemctl status redis-server
因此,Redis 服务已在 Ubuntu 20.04 Server 上启动并运行。
现在使用下面的 netstat 命令检查默认的 Redis 端口 6379。
ss -plnt4你会得到 Redis 服务在默认 6379 的本地主机 IP 地址上运行的结果。
现在使用 redis-cli 命令检查 Redis,如下所示。
redis-cli ping
redis-cli ping "Hello Redis"你会得到如下结果。
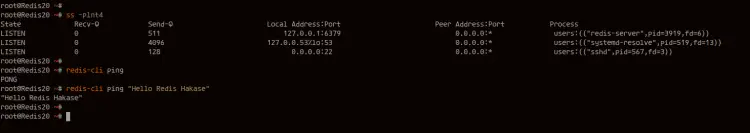
如果您的安装正确,您将收到带有 PONG 的 Redis 服务器回复,或回复您在 ping 选项后输入的文本。
Redis Server 的基本安装和配置已经成功完成。
第 3 步 - 保护 Redis 安装
在此步骤中,我们将保护我们的 Redis 安装。关于保护 Redis 服务器,您必须了解 3 件事。
1. 网络安全
Redis服务器的网络安全与Redis配置redis.conf中的bind配置有关。建议使用内部专用网络安装 Redis,不要使用公共网络。
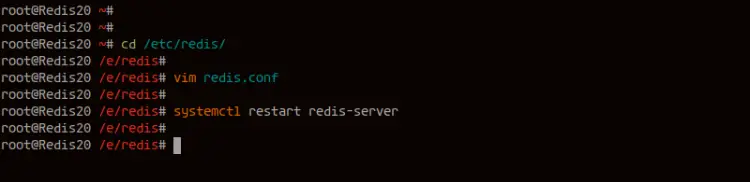
进入/etc/redis目录,编辑配置文件redis.conf。
cd /etc/redis/
vim redis.conf在绑定部分,将 IP 地址更改为您自己的内部网络 IP 地址。
bind INTERNAL-IP-ADDRESS保存并关闭。
现在 Redis 服务将在 INTERNAL-IP-ADDRESS 下运行。
2. 密码认证
Redis 的密码身份验证将为您提供对 Redis 服务器的访问控制。这是一个小的安全层,可以增强您的 Redis 服务器的安全性,默认安装尚未启用。
要为 Rediser 服务器启用密码身份验证,您需要取消 redis.conf 文件中 requirepass 部分的注释并在其后键入您的强密码。
requirepass HakaseLabsRedisPasswd使用您的强密码更改 HakaseLabsRedisPasswd。至此Redis的密码认证已经开启。
3.禁用危险的Redis命令
Redis 提供了禁用某些特定 Redis 命令的功能。此功能可用于重命名或禁用一些危险命令,例如用于擦除所有数据的 FLUSHALL、用于通过 Redis CLI 设置配置参数的 CONFIG 命令等。
要更改或禁用 Redis 命令,您可以使用重命名命令选项。编辑Redis配置文件redis.conf,在下面添加一些配置。
# rename-command COMMAND "CUSTOM"
rename-command FLUSHALL "DELITALL"
rename-command CONFIG "MYSERVERCONF"保存并关闭。
全部完成后,使用下面的 systemctl 命令重新启动 Redis 服务。
systemctl restart redis-server用于保护 Redis 安装的基本 Redis 安全性已应用于我们的主机。
其他考虑,您可能还需要 Redis 的数据加密支持,以及应用程序端所需的安全编码。
第 4 步 - 测试
在此步骤中,我们将使用 redis-cli 命令行测试我们的 Redis 服务器部署。
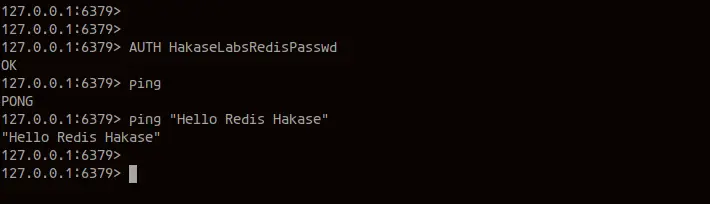
1.测试主机和认证
通过指定 redis 服务器主机名/IP 地址和端口,使用 redis-cli 命令连接到 Redis 服务器。
redis-cli -h 127.0.0.1 -p 6379将 127.0.0.1 更改为您自己的 IP 地址。
连接到服务器后,请尝试 ping 命令。
ping
ping "Hello Redis"现在您将得到如下结果。
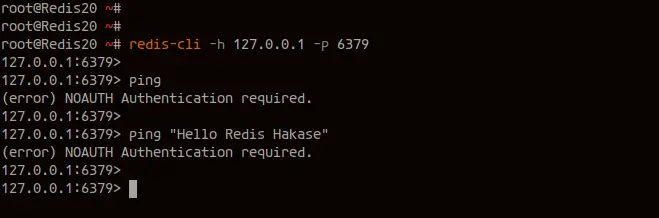
您收到错误是因为在 Redis CLI shell 上调用任何命令之前需要进行身份验证。
运行以下命令以针对 Redis 服务器进行身份验证。
AUTH HakaseLabsRedisPasswd通过身份验证后,您可以尝试执行 ping 命令,您将获得 Redis 服务器的回复。
ping
ping "Hello Redis"以下是您通过 Redis 服务器身份验证后的结果。
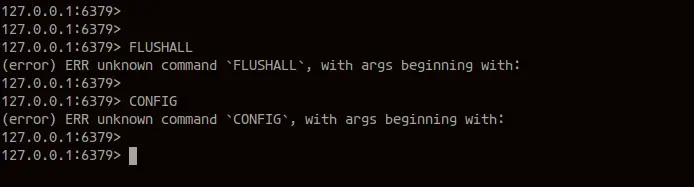
2.测试禁用/重命名命令
运行我们在 shell 上重命名的所有命令,您将收到命令错误。
FLUSHALL
CONFIG下面是这些命令的错误结果。
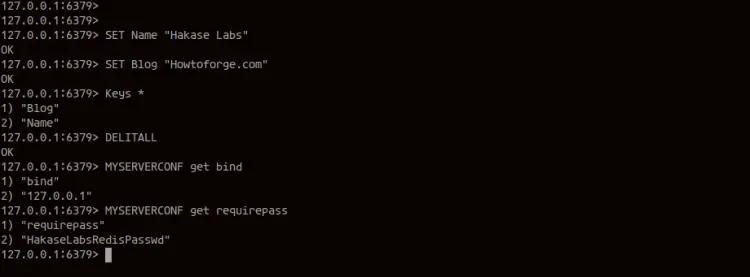
接下来,为每个运行自定义命令。
使用 redis-cli 命令创建新密钥,如下所示。
SET Name "Hakase Labs"
SET Blog "Howtoforge.com"
Keys *现在使用重命名的 FLUSHALL 命令 DELITALL 删除所有键和数据。
DELITALL对于 CONFIG 命令,您可以尝试检索或设置 Redis 服务器配置的新值。 CONFIG 命令重命名为 MYSERVERCONF。
MYSERVERCONF get bind
MYSERVERCONF get requirepass下面是这些新重命名的自定义命令的结果。
Ubuntu 20.04 Redis Server 基础安装已经完成,Redis Server 的基础安全已经应用。
参考
- https://redis.io/documentation
