如何在 Ubuntu 18.04 LTS 上安装和配置 Mantis Bug Tracker
Mantis 是一个免费的开源错误跟踪基于 Web 的应用程序工具,适用于 Windows、OS X 和 Linux。它是用 PHP 编写的,支持不同类型的数据库。 Mantis Bug Tracker 也称为 MantisBT。
MantisBT 使用简单,具有许多功能,例如
- 用户可以自定义问题创建/查看/问题工作流程以及通知的字段
- Mantis 支持发布功能以管理项目的各种发布
- 与团队成员和客户轻松协作
- 通过电子邮件报告问题
- 每当对问题进行任何更改时发送电子邮件通知
- 易于使用的仪表板
- 基于用户的访问级别,用户可以针对不同的项目拥有不同类型的访问级别
- 支持大量插件
在本教程中,我们将学习如何在 Ubuntu 18.04 LTS 上安装 MantisBT。
先决条件
具有最小安装的 Ubuntu 18.04 操作系统。
具有 root 权限的 sudo 用户。
1 入门
首先,使用 sudo 权限登录到您的服务器,并使用以下命令将系统更新为最新的稳定版本:
sudo apt update && apt upgrade -y2 安装LAMP服务器
Mantis 需要在您的服务器上安装 Apache2、PHP 和数据库服务器。
安装 Apache Web 服务器
您可以通过以下命令安装 apache 网络服务器:-
sudo apt install apache2 -y现在让我们检查 apache 服务
sudo systemctl status apache2如果 apache 网络服务器未运行,则运行以下命令
sudo systemctl start apache2现在通过运行以下命令使 apache 服务在引导时启动:
sudo systemctl enable apache2安装PHP
Mantis 是用 PHP 编写的,因此您需要在系统中安装 PHP 和其他必需的模块。在终端中运行以下命令
sudo apt install wget php php-cli php-fpm php-mysql php-zip php-gd php-mbstring php-curl php-xml php-pear php-bcmath现在通过以下命令检查 PHP 的版本
php -v你会看到类似的输出
PHP 7.2.24-0ubuntu0.18.04.1 (cli)(内置:2019 年 10 月 28 日 12:07:07)( NTS )
版权所有 (c) 1997-2018 The PHP Group
Zend Engine v3.2.0,版权所有 (c) 1998-2018 Zend Technologies
Zend OPcache v7.2.24-0ubuntu0.18.04.1,版权所有 (c) 1999-2018,Zend Technologies
现在您可以通过编辑以下文件来调整 PHP 设置。
sudo vim /etc/php/7.2/apache2/php.ini根据您的要求设置上传文件大小
upload_max_filesize = 50M为 Mantis 安装和配置数据库服务器
接下来,运行以下命令来安装 MariaDB 服务器。
sudo apt install mariadb-server mariadb-client现在启动 MariaDB 服务并使其在启动时启动,然后使用以下命令检查 MariaDB 服务状态:
sudo systemctl start mariadb
sudo systemctl enable mariadb
sudo systemctl status mariadb接下来,使用以下命令保护 MariaDB 安装:
sudo mysql_secure_installation回答以下所有问题:
Set root password? [Y/n] Y
New password:
Re-enter new password:
Remove anonymous users? [Y/n] Y
Disallow root login remotely? [Y/n] Y
Remove test database and access to it? [Y/n] Y
Reload privilege tables now? [Y/n] Y您的 MariaDB 安装现在是安全的。
接下来,登录到 MariaDB 控制台,如下所示:
sudo mysql -u root -p出现提示时输入您的根密码。
注意:- 如果您在没有 sudo 的情况下无法登录到 mysql,并且它显示错误 1698 (28000):用户 root@localhost 拒绝访问
对于此错误,请运行以下命令
sudo mysql -u root
mysql> USE mysql;
mysql> UPDATE user SET plugin=mysql_native_password WHERE User=root;
mysql> FLUSH PRIVILEGES;
mysql> exit;
sudo systemctl 重启 mariadb
接下来,为 Mantis 创建一个数据库:
MariaDB [(none)]> CREATE DATABASE mantisdb;接下来,使用以下命令创建用户和密码:
MariaDB [(none)]>CREATE USER 'mantis'@'localhost' IDENTIFIED BY 'mentispassword';然后使用以下命令授予 mantisdb 数据库权限:
MariaDB [(none)]>GRANT ALL PRIVILEGES ON mantisdb.* TO 'mantis'@'localhost' IDENTIFIED BY 'mentispassword' WITH GRANT OPTION;接下来,运行以下命令重新加载权限表
MariaDB [(none)]>FLUSH PRIVILEGES;现在使用以下命令从 MariaDB 控制台运行退出:
MariaDB [(none)]>exit;安装螳螂BT
您可以从他们的官方网站下载最新版本的螳螂。您可以使用 wget 命令下载它:
wget https://excellmedia.dl.sourceforge.net/project/mantisbt/mantis-stable/2.22.1/mantisbt-2.22.1.zip下载 Mantis BT 后,解压下载的文件并使用以下命令将其移动到 apache web 根目录:
unzip mantisbt-2.22.1.zip
sudo mv mantisbt-2.22.1 /var/www/html/mantis/Next 为 mantis 目录设置适当的权限
sudo chown -R www-data:www-data /var/www/html/mantis接下来,运行以下命令为 Mantis 创建一个 apache 虚拟主机文件。
sudo vim /etc/apache2/sites-available/mantis.conf现在在 mantis.conf 中添加以下行
<VirtualHost *:80>
ServerAdmin
DocumentRoot "/var/www/html/mantis"
ServerName yourdomain.com
ServerAlias www.yourdomain.com
ErrorLog "/var/log/apache2/mantis-error_log"
CustomLog "/var/log/apache2/mantis-access_log" combined
<Directory "/var/www/html/mantis/">
DirectoryIndex index.php index.html
Options FollowSymLinks
AllowOverride All
Require all granted
</Directory>
</VirtualHost>保存并关闭文件。然后使用以下命令启用虚拟主机。
sudo a2ensite mantis.conf最后,通过运行以下命令重新启动 apache 服务。
sudo systemctl restart apache2配置防火墙
对于 Mantis BT,您需要允许端口 80 通过 UFW 防火墙。您可以启用 UFW 防火墙并通过以下命令检查其状态:
sudo ufw enable
systemctl status ufw接下来,通过以下命令允许端口 80
sudo ufw allow 80访问 Mantis BT Web 界面
打开您的 Web 浏览器并输入 URL http://yourdomain.com,您应该会看到以下页面:
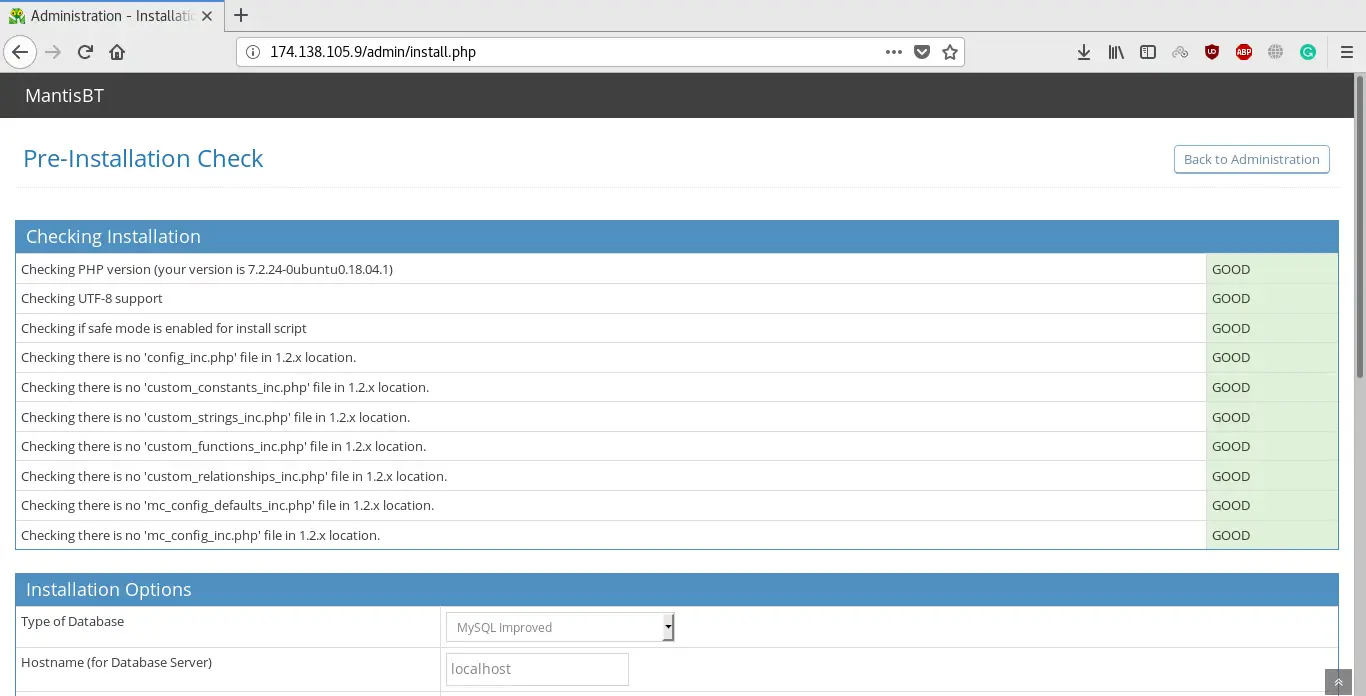
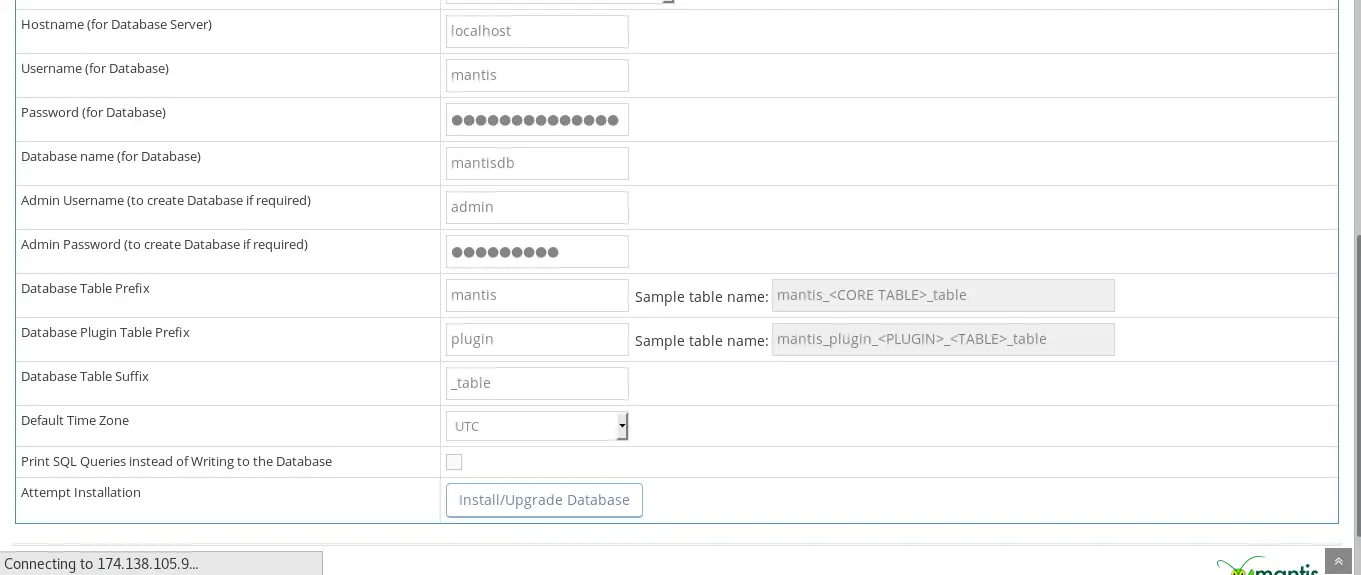
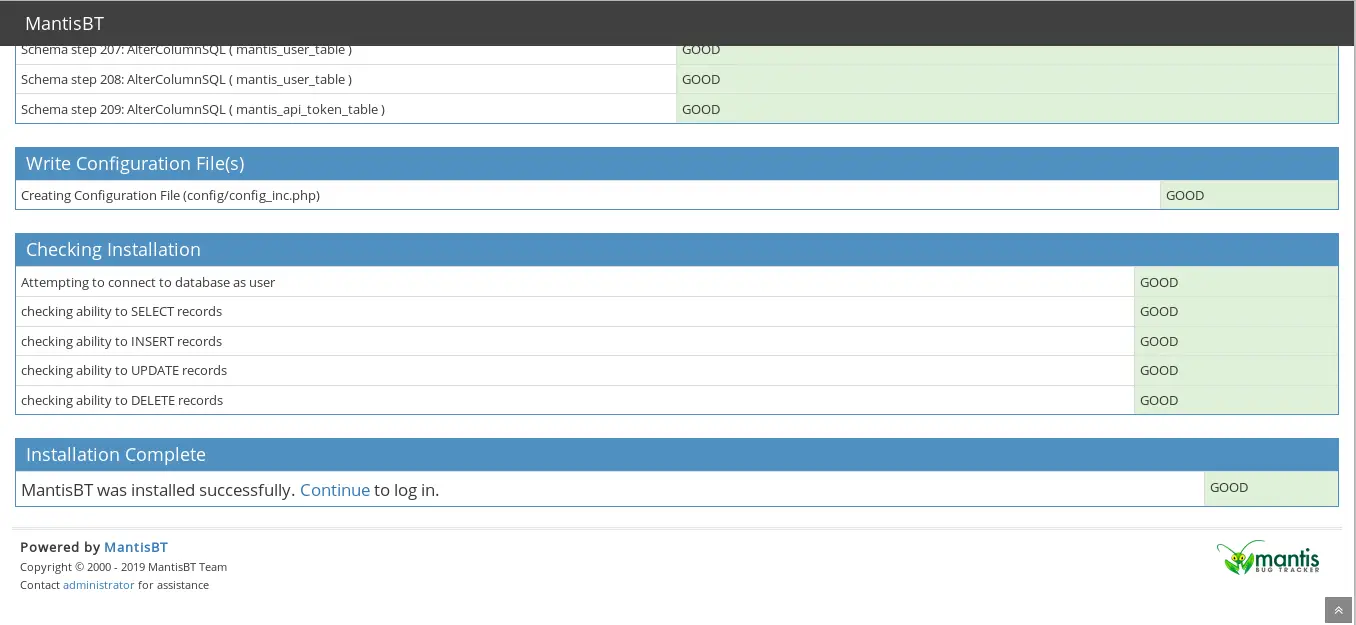
现在,提供所有必需的信息,例如数据库名称、数据库用户名、密码、管理员用户名和密码。然后单击“安装/升级”数据库按钮。安装完成后,您应该会看到以下页面:
接下来,点击“继续”按钮,您应该会看到如下所示的 Mantis BT 登录页面
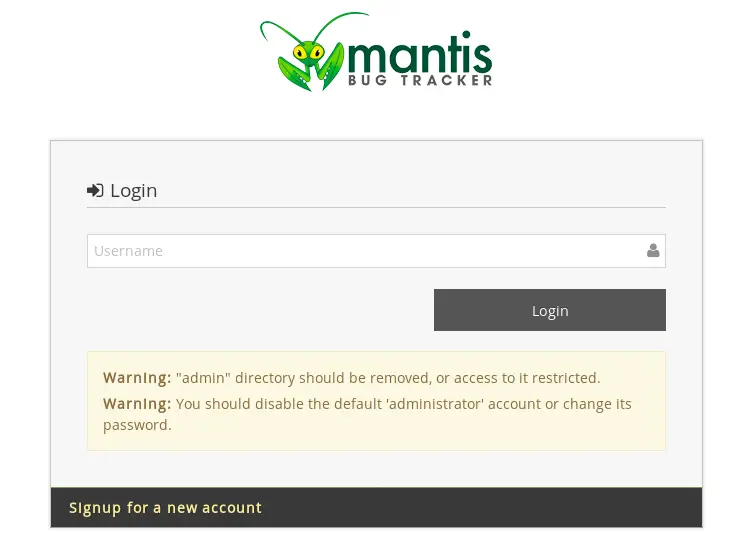
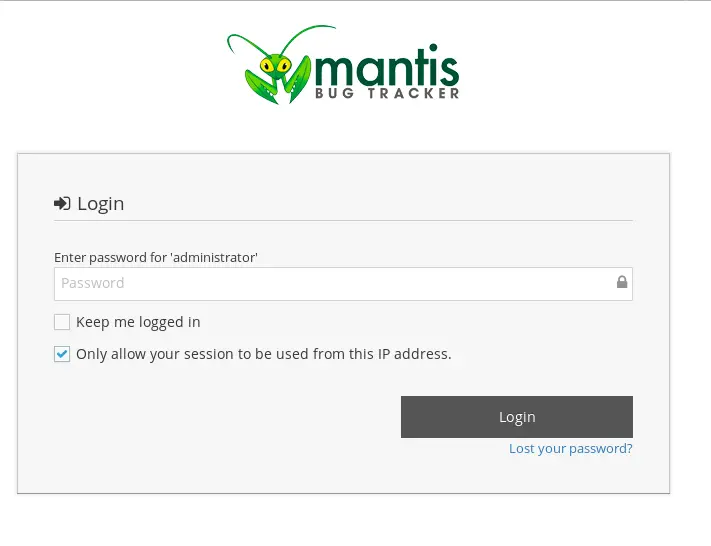
提供默认的 Mantis BT 用户名“administrator”和密码“root”。然后单击“登录”按钮,您应该会在下图中看到 Mantis BT 仪表板:
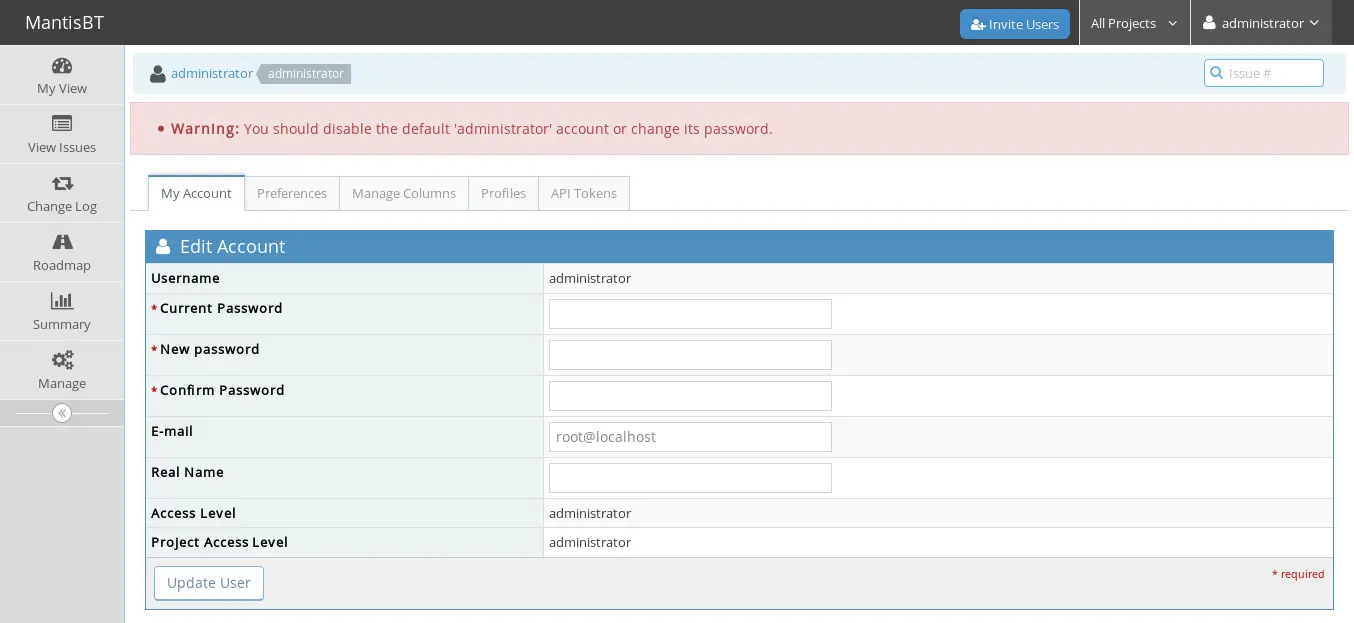
最后,您已经在 Ubuntu 18.04 服务器上成功安装了 Mantis BT。
